March 16th, 2026 - March 16, 2026: SCIM Support, Incident Response Guide, Splunk Integration Updates and more
📢 Google TI Mondays. Quick reminder to Follow the Google TI Mondays series across our social platforms every week for quick, actionable practitioner tips and product adoption advice designed to enhance your efficiency. These actionable tips are essential. #GoogleTIMondays
📢 New Adoption Guide: Introduction to Incident Response with Google Threat Intelligence. We’ve released a step-by-step operational playbook with a Remcos RAT infection as a blueprint. This guide walks you through rapid triage and complex payload analysis to streamline your incident response.
💪 Detection Highlights. This week, the Google Threat Intelligence Group and FLARE team have enhanced Google TI's detection capabilities by releasing YARA rules for 4 newly tracked malware families and updating detection content for 28 existing families. This includes expanding our configuration extraction platform to cover 1 new malware family. Our prioritization for new and updated detection content focuses on malware actively observed in Mandiant incident response engagements, Google SecOps customer environments, and top Google TI search trends.
As we track new malware families found through our research, we build and release detection signatures. Some recent examples include:
- DINODANCE: operates by utilizing an MSI installer to drop VBScript and PowerShell components. The VBS component executes the PowerShell component through the Shell.Run method, while the PowerShell component downloads and installs Deno, a JavaScript runtime environment, to execute the embedded JavaScript component. See its curated YARA detection rules.
- SKIPIPE: a backdoor with the capability to download a second stage, communicate with a command and control (C2 or C&C), establish named pipes, and execute commands on a compromised system. See its curated YARA detection rules.
- GHOSTBLADE: a dataminer written in JavaScript that collects and exfiltrates a wide variety of data from a compromised device, including messages, account/device identifiers, photos, files, cryptocurrency wallet data, and more. GHOSTBLADE must be deployed following a successful exploit chain building arbitrary kernel memory read/write primitives to function properly. Data collected by GHOSTBLADE is exfiltrated to an attacker-controlled server over HTTP(S). See its curated YARA detection rule.
In addition to providing detection rules for new and emerging threats, we continue to update our detection systems for known threats like HAVOCDEMON, COOLWIPE, and CHILLWIPE. These updates ensure you have the latest YARA signatures and configuration extraction capabilities.
See latest malware family profiles added to the knowledge base and the complete list of curated YARA rules in our database.
🔄 Google TI Integration Guide for Splunk. The Google TI App for Splunk bridges Google TI’s massive threat repository with Splunk. It enables real-time correlation of internal logs with global intelligence, automatically enriching events, including IPs, domains, URLs, and hashes, with reputation scores and threat categories to accelerate triage and eliminate manual research. We have published a significantly more detailed Integration Guide, which provides a comprehensive, step-by-step walkthrough for security administrators.
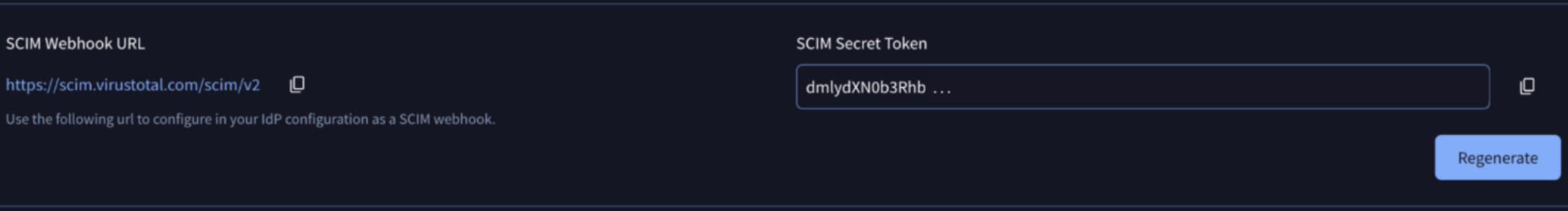
🆕 Automated User Deprovisioning via SCIM. Google TI now supports SCIM (System for Cross-domain Identity Management), a standard protocol used to automate the exchange of user identity information between identity domains and IT systems. This integration acts as a webhook that connects your Identity Provider (IdP) directly to your organization’s group management settings, to automatically removes deactivated users from your Google TI group, ensuring that former employees or unauthorized users lose access to sensitive threat intelligence.