April 6th, 2026 - AutoIt Deobfuscation for Agentic, Improved RBAC, and more
📢 Google TI Mondays. Quick reminder to Follow the Google TI Mondays series across our social platforms every week for quick, actionable practitioner tips and product adoption advice designed to enhance your efficiency. These actionable tips are essential. #GoogleTIMondays
💪 Detection Highlights. The Google Threat Intelligence Group and FLARE team continue to expand Google TI's detection capabilities through the development of YARA rules and malware configuration extractors. This week, we have introduced YARA rules for 8 newly tracked malware families and updated configuration extraction support for 2 existing families. Our team prioritizes the creation of this content based on threats identified during Mandiant incident response engagements, activity within Google SecOps customer environments, and trending searches within Google TI.
As our research uncovers new malware families, we develop and deploy detection signatures to provide immediate visibility. Recent additions include:
- WAVESHAPER.V2: a cross-platform backdoor family targeting Windows, Linux, and macOS. It is identified by a standardized Command and Control (C2) architecture featuring a 60-second beaconing interval, 16-character unique victim IDs, and a platform-agnostic User-Agent used for all C2 communication. This shared framework enables consistent remote capabilities across all variants, including host reconnaissance, directory enumeration, and the staging of secondary scripts or binaries. See its curated YARA detection rule.
- MOONBOX: a ransomware written in C++ that encrypts both documents and database files along with virtual machine related files. The ransomware uses the ChaCha20 stream cipher algorithm for file encryption, generating a unique key for each file which is then encrypted using an embedded RSA public key and appended to the locked file. The ransomware accepts multiple command-line arguments to modify its behavior, including "--fast" to encrypt only the first 1MB of files, "--gpo" to spread the ransomware via Group Policy Object, and "--psexec" to attempt self-propagation within the network. MOONBOX drops a ransom note named "YOU ARE UNDER ATTACK!.html". In some cases the target files are appended with the ".locked" extension while in other analyzed samples encrypted files are appended with the ".exitium" file extension.
- SILKBELL: an obfuscated dropper written in JavaScript deployed inside malicious NPM packages. The dropper is capable of profiling the victim's operating system (Windows, Linux, or macOS) and downloadING secondary payloads. See its curated YARA detection rules.
Beyond tracking new threats, we consistently refine our detections for established malware to ensure high-fidelity intelligence. We have recently updated our detection and configuration extraction coverage for SYSTEMBC.LINUX and ROADSIGN. These updates provide users with the most current indicators and extracted configurations to better defend against persistent threats.
See latest malware family profiles added to the knowledge base and the complete list of curated YARA rules in our database.
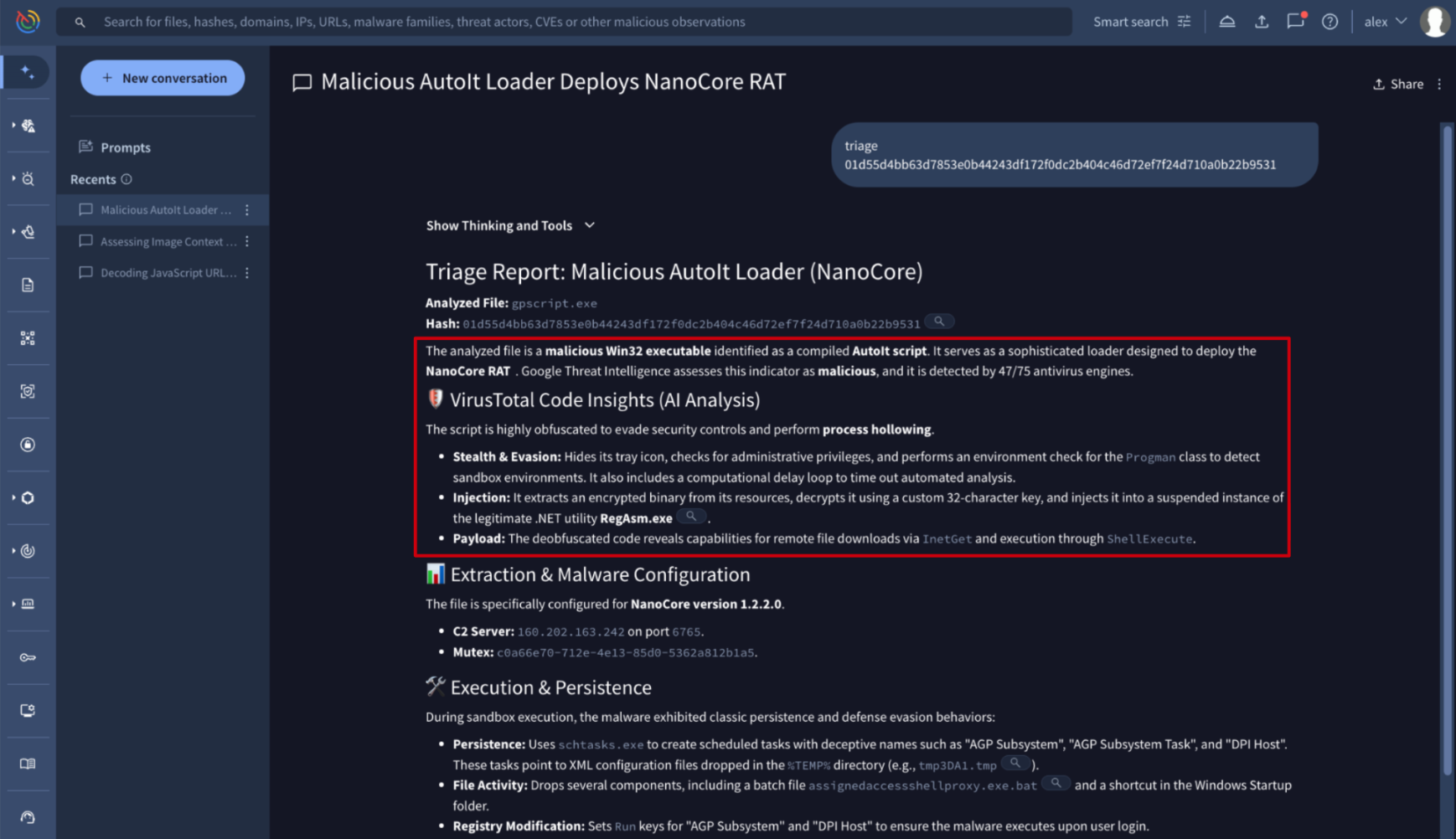
💪 Unmasking Obfuscated Malware: Agentic Now Supports AutoIt Deobfuscation. Agentic is the conversational AI platform for Google Threat Intelligence that coordinates specialized security agents for advanced malware analysis. By leveraging Code Insight, an AI-driven analysis engine, it can now interpret the logic of AutoIt-compiled executables. This process automatically extracts and deobfuscates the underlying source code, which is a critical step since attackers frequently use AutoIt to hide malicious intent.
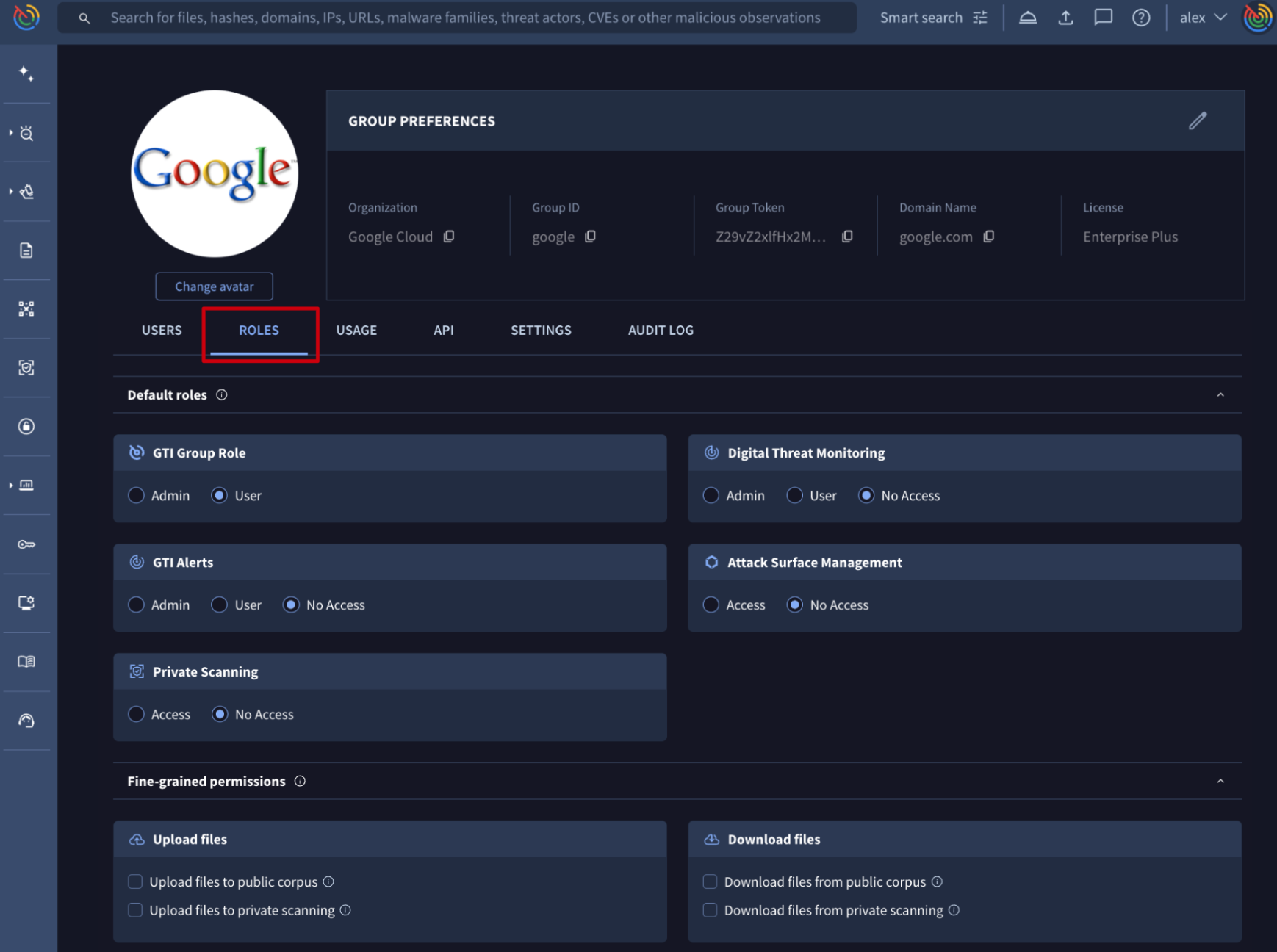
🔄 Improved Role-Based Access Control Management. The Group Management suite within the Google Threat Intelligence platform allows administrators to oversee their organization’s users, service accounts, features allowance and consumption and all group settings. It provides a centralized interface to control who has access to the platform and what specific modules they can interact with.
Group administrators can now define preset roles and permissions that are automatically assigned to new members. While these settings apply by default, administrators retain the flexibility to manually override them for individual or bulk onboarding via the Add User form.